One of the biggest and scariest fraud threats is having your account taken by a fraudster. In this article, we will discuss the top takeover fraud scenarios that may lead to fraudsters accessing and having control of your assets.
Table of Contents
ToggleWhat is account takeover (ATO) fraud?
Account takeover fraud, also known as account compromise, refers to fraud which occurs when a fraudster gains access to a legitimate user’s account to make unauthorised transactions.
Fraudsters take over online accounts using stolen credentials such as passwords and usernames. Fraudsters buy credentials on the dark web, usually through social engineering, data breaches, and phishing attacks. They use these credentials to deploy bots that test passwords and username combinations on travel, retail, finance, eCommerce, and social media sites.
Attackers compile a list of validated credentials and sell or abuse them to make a profit. Fraudsters can also commit identity fraud through ATO fraud, causing identity theft as they use someone’s personal details to commit fraud.
Users rarely change passwords and reuse login information. Bots can carry credential stuffing and brute force assaults to take over accounts. Cybercriminals can also hack mobile sites, webpages, and native mobile APIs.
How does ATO work?
Below are the typical steps involved in an ATO attack:
- Information gathering: Attackers begin by collecting information about their target, which may include usernames, email addresses, passwords, and any other personal data available through various means such as phishing emails, social engineering tactics, or data breaches.
- Credential stuffing: Armed with the acquired login credentials, attackers use automated scripts or tools to systematically test combinations of usernames and passwords across multiple websites or online services. This technique, known as credential stuffing, takes advantage of users who reuse passwords across different platforms.
- Brute Force attacks: In some cases, attackers resort to brute force attacks, where they repeatedly try different combinations of usernames and passwords until they successfully gain access to the targeted account. This method is time-consuming but can be effective, especially against weak or commonly used passwords.
- Phishing and social engineering: Attackers may also employ phishing techniques, sending deceptive emails or messages that appear to be from legitimate sources, tricking users into revealing their login credentials or other sensitive information voluntarily. Social engineering tactics exploit human psychology to manipulate users into divulging confidential data.
- Account takeover: Once the attackers gain access to a user’s account, they can carry out various fraudulent activities, such as making unauthorized purchases, stealing sensitive information, initiating financial transactions, or perpetrating identity theft. They may also hijack the account to launch further attacks, distribute spam, or spread malware.
- Covering tracks: To avoid detection and prolong their access, attackers may attempt to cover their tracks by altering account settings, deleting logs, or masking their IP addresses using proxy servers or virtual private networks (VPNs).
By understanding the methods and techniques used in ATO fraud, users can take proactive measures to protect their accounts, such as using strong, unique passwords, enabling multi-factor authentication (MFA), staying vigilant against phishing attempts, and regularly monitoring their online accounts for any suspicious activity.
Why is it important to detect ATO attacks?
Detecting ATO (Account Takeover) attacks is crucial for several reasons, including:
- Protecting user data and privacy: ATO attacks often result in unauthorized access to sensitive user information, such as personal details, financial data, or confidential communications. Detecting and mitigating these attacks promptly helps safeguard user privacy and prevent the misuse or exploitation of their data.
- Preventing financial losses: Account takeovers can lead to financial losses for both individuals and businesses. Attackers may use compromised accounts to make fraudulent purchases, transfer funds, or engage in other illicit financial activities. By detecting ATO attacks early, organizations can minimize financial damages and prevent unauthorized transactions.
- Preserving reputation and trust: A successful ATO attack can damage an organization’s reputation and erode customer trust. Instances of data breaches or compromised accounts can undermine confidence in the security measures implemented by businesses, leading to negative publicity and customer churn. Detecting and addressing ATO attacks promptly demonstrates a commitment to security and helps maintain trust with stakeholders.
- Preventing further compromise: A compromised account can serve as a foothold for attackers to launch additional cyberattacks or exploit other vulnerabilities within an organization’s network. Detecting ATO incidents allows security teams to identify and mitigate potential security weaknesses, preventing further compromise and limiting the extent of the damage.
- Compliance requirements: Many industries are subject to regulatory requirements and compliance standards governing data protection and cybersecurity. Detecting and responding to ATO attacks promptly is essential for meeting regulatory obligations and avoiding potential penalties or legal consequences associated with data breaches or unauthorized access incidents.
- Enhancing security posture: Proactively detecting and mitigating ATO attacks helps organizations strengthen their overall security posture. By analyzing attack patterns and identifying common tactics used by adversaries, security professionals can implement proactive measures to enhance security controls, improve threat detection capabilities, and better protect against future attacks.
In conclusion, detecting ATO attacks is essential for safeguarding user data, preventing financial losses, preserving reputation and trust, complying with regulatory requirements, and enhancing overall security resilience.
Attack methods used in account takeover fraud
Credentials are critical to a successful account takeover. Below are several ways hackers take over a valid account:
- Brute-force attacks: These include password spraying and credential stuffing (guessing complete credential pairs). The attacker tries a username/password combination on several accounts until one works. Attackers utilise common passwords and dictionary terms to guess passwords.
- Breach replay attack/credential stuffing: Many people reuse passwords across accounts, which is a bad practice. Any online account with the same username, email address, and the same password is at risk of one of these frauds.
- Phishing. Credential phishing is a practical approach to stealing a victim’s password. Phishing primarily affects accounts without multi-factor authentication (MFA).
- Malware attacks: Keyloggers, stealers, and other malware are used to expose user passwords, giving attackers account access.
- Credential stuffing: Attackers leverage lists of previously compromised credentials to automate login attempts across multiple websites, exploiting users who reuse passwords.
- SIM card swapping: Attackers deceive mobile network providers into transferring a victim’s phone number to a SIM card under their control, allowing them to receive authentication codes and take over accounts linked to the victim’s phone number.
- Mobile banking trojans: Malicious software designed to infiltrate mobile devices, particularly targeting banking and financial apps, enabling attackers to intercept sensitive information such as login credentials and transaction data.
- Man-in-the-Middle attacks: Hackers intercept communication between the user and the legitimate service, allowing them to eavesdrop on sensitive information, manipulate data, or impersonate either party to gain unauthorized access to the account, leading to Man-in-the-Middle attacks.
Impacts of account takeover fraud
Account Takeover (ATO) fraud can have significant consequences for individuals, businesses, and society as a whole. Below are some of the key impacts associated with ATO fraud:
- Financial losses: ATO attacks can result in financial losses for both individuals and businesses. Attackers may exploit compromised accounts to make unauthorized purchases, transfer funds, or conduct fraudulent transactions, leading to monetary losses for victims and organizations.
- Identity theft: A successful ATO attack can facilitate identity theft, where attackers assume the identity of the account holder to engage in further fraudulent activities. This can have long-term repercussions for victims, including damage to their credit history, financial reputation, and personal wellbeing.
- Data breaches: ATO incidents often involve the unauthorized access and exfiltration of sensitive data stored within compromised accounts. This can lead to data breaches, exposing personal information, financial records, and other confidential data to unauthorized parties, resulting in privacy violations and regulatory repercussions.
- Reputational damage: ATO attacks can tarnish the reputation of businesses and organizations, eroding customer trust and confidence in their security measures. Instances of data breaches or compromised accounts may lead to negative publicity, loss of credibility, and diminished brand loyalty, impacting long-term relationships with stakeholders.
- Disruption of services: In some cases, ATO attacks may disrupt the normal functioning of online services or systems, causing inconvenience to users and operational disruptions for businesses. Account takeovers can result in account lockouts, suspension of services, or unauthorized changes to account settings, affecting productivity and customer satisfaction.
- Legal and regulatory consequences: Organizations that fail to adequately protect against ATO fraud may face legal and regulatory consequences, including fines, penalties, and legal liabilities. Compliance with data protection regulations and cybersecurity standards is essential to mitigate the risk of regulatory enforcement actions and legal disputes arising from ATO incidents.
- Emotional and psychological impact: ATO fraud can have a profound emotional and psychological impact on victims, causing stress, anxiety, and feelings of vulnerability. The loss of control over personal information and financial assets can lead to emotional distress and trauma, affecting the overall wellbeing and mental health of individuals.
By understanding the wide-ranging impacts of ATO fraud, individuals and organizations can take proactive measures to enhance their cybersecurity defenses, implement robust authentication mechanisms, and mitigate the risk of account compromise.
Top 5 Account Takeover fraud scenarios
The methods discussed above are used in ATO and can lead to many account takeover scenarios, with the most common being the following 5:
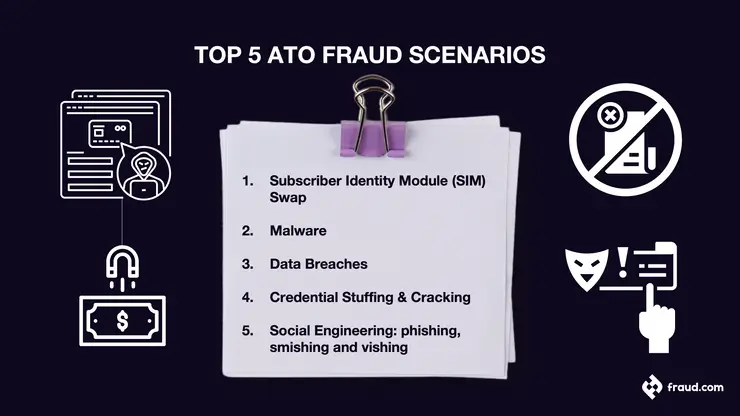
Subscriber Identity Module (SIM) Swap
SIM swap fraud occurs when con artists use your phone number to access your accounts.
SIM swap occurs when criminals call your cell service provider to activate a new SIM card. Fraudsters will then control your phone number. Calls and text messages to your number are routed to the fraudsters’ device rather than yours.
By committing SIM swap fraud, con artists can access your accounts, such as bank credentials. The Hacker will try to access your accounts, and if you have 2-factor authentication, the code will be sent to your sim card via text message. Unfortunately, the fraudsters will be the ones with access to your sim.
SIM swap is avoidable. It involves preventing unauthorised access to your online accounts, such as banking details and credit card accounts. Also, keep an eye out for SIM swap warning indicators.
Malware
Account takeover fraudsters use social engineering techniques such as malware, pop-ups, and so on to infect vulnerable machines in your network. A malware replay attack is one of the most used account takeover attacks.
Once your device has been infected, cybercriminals can use the malware to steal login credentials or perform a replay attack.
During a replay attack, attackers capture data packets transferred from your network to a financial institution and modify and retransmit it.
The good news is that detecting a malware attack is possible. Below are some of the warning indications for a malware attack:
- Your system becomes slower: Malware usually uses system resources, hence making it to be slower
- A sudden increase in traffic
- Sudden receiving of unfamiliar error messages
- Receiving spam emails
- Unusual ads and pop-ups
Data breaches
Every year, billions of personal information documents are stolen in data breaches. Data breaches might include usernames, passwords, and occasionally even secret answers.
The disclosed usernames and passwords are sometimes all hackers need to take over accounts.
Since most individuals use the same login credentials for several accounts, hackers will attempt to access additional online services using the same compromised passwords and usernames.
Credential stuffing & cracking
Credential stuffing is excellent for use against online shops. It is a low-cost and low-effort attack technique that is far simpler to execute on a big scale for a lesser payoff across several victim accounts. In this process, the fraudster deploys an automated tool or script to perform login requests using the compromised credentials to acquire access to user accounts.
The tool analyses the username and password combinations against a login page. This analysis is like having many keys and trying each on the front door of a residence. With credential stuffing, you are more likely to have the correct ‘key’ due to the repetition of passwords, which is why users should not use repetitive password across account and make sure to use strong passwords.
Social engineering
Social engineering is a broad category of malicious operations carried out through human interaction. It utilises psychological manipulation to deceive users into committing security errors or disclosing sensitive information.
Social engineering attacks can happen through phishing, smishing and vishing, and consists of multiple phases. A perpetrator initially analyses the intended victim to obtain background information, such as potential entry points and weak security protocols required to proceed with the attack. The attacker attempts to acquire the victim’s trust and give stimuli for later acts that violate security norms, such as disclosing sensitive information or granting access to vital resources.
Social engineering is extremely harmful because it relies on human error rather than software or operating system weaknesses. Legitimate user errors are significantly less predictable, making them more challenging to detect and prevent than malware-based intrusions.
Social engineering theft usually utilises three main types of account takeover. These are:
Phishing
Phishing is a fraudulent attempt to obtain your valuable personal information. In many cases today, this is accomplished using phishing emails.
Smishing
Smishing is a form of phishing that uses text messages or short messaging systems. Frequently, you will receive a message from a bank or service provider requesting that you check in to a specific website or dial a particular number.
Vishing
Vishing is another form of phishing that uses phone calls to solicit sensitive personal information. This is becoming highly common as people are becoming more lenient and view phone calls as more authentic than emails.
Account takeover protection methods
Protecting against account takeover (ATO) fraud requires a multi-layered approach. Here are key methods to safeguard user accounts:
- Multi-Factor Authentication (MFA): Require multiple forms of verification, such as passwords and one-time codes, to access accounts, making it harder for attackers to compromise credentials.
- AI-based detection: Use artificial intelligence and machine learning algorithms to analyze user behavior and detect suspicious activity in real-time, enhancing fraud detection capabilities.
- Web Application Firewall (WAF): Deploy a WAF to monitor and filter incoming web traffic, blocking common ATO attack vectors like credential stuffing and SQL injection.
- Device recognition and IP geolocation: Track user devices and IP addresses to detect unauthorized access attempts from unfamiliar locations, enabling proactive security measures.
- Account tracking system: An account tracking system monitors user activities, like logins, settings changes, and transactions, to spot suspicious behavior. It analyzes activity patterns, such as unfamiliar logins or unusual transactions, triggering alerts for investigation and preventing ATO incidents.
- Behavioral biometrics: Analyze unique user behavior patterns, such as typing speed and mouse movements, to authenticate users and detect anomalies indicative of ATO fraud.
- Security awareness training: Educate users about common ATO tactics and promote security best practices to mitigate risks associated with phishing scams and password reuse.
By implementing these methods, organizations can strengthen their defenses against ATO fraud and protect user accounts from unauthorized access.
Best practices to detect and prevent ATO
Account takeover differs from regular online payment fraud in appearance. Monitoring login rates, devices, and customer credentials are essential. One of the best ways to detect and prevent ATO is by leveraging the use of machine learning (ML) to create different ML models to best suit the fraud prevention and detection needs based on the historical data held.
2020-2021 UK Statistics shows that there has been an increase of 125,000 identity theft within two years, which led to over £2.3bn loss.
Here are some methods for preventing or containing an attack.
- Cross-reference login information with existing records
- Look for breached credentials
- Verify a user’s identity whenever they modify any account information
- Send users notices about account modifications
How banks can help prevent Account Takeover fraud
Banks play a crucial role in safeguarding their customers’ accounts and preventing account takeover (ATO) fraud. Here are some strategies banks can implement to enhance security and protect against ATO attacks:
- Multi-Factor Authentication (MFA): Banks can implement Multi-Factor Authentication (MFA) mechanisms that require customers to provide multiple forms of identification before granting access to their accounts. This typically involves a combination of something the user knows (e.g., password), something they have (e.g., mobile device for receiving one-time codes), or something they are (e.g., biometric authentication).
- Continuous monitoring and anomaly detection: Banks can employ fraud detection systems powered by Artificial Intelligence (AI) and Machine Learning (ML) that continuously monitor account activity for suspicious behaviour and anomalies. These systems analyze transaction patterns, login locations, device fingerprints, and other factors to identify potential ATO attempts in real-time.
- Customer education and awareness: Banks can educate their customers about the risks of ATO fraud and provide guidance on best practices for securing their accounts. This may include tips on creating strong passwords, avoiding phishing scams, enabling account alerts, and regularly monitoring account activity for unauthorized transactions.
- Real-time alerts and notifications: Banks can offer real-time alerts and notifications to customers for any changes or transactions occurring in their accounts. These alerts can help customers quickly identify and respond to suspicious activity, such as unauthorized logins, password changes, or large transfers.
- Secure communication channels: Banks should ensure that communication channels used for customer interactions, such as email, chat, or phone, are secure and encrypted to prevent interception or manipulation by attackers. Customers should be encouraged to verify the authenticity of communications before providing any sensitive information.
- Fraud prevention partnerships: Banks can collaborate with industry partners, cybersecurity firms, and law enforcement agencies to share threat intelligence, identify emerging fraud trends, and coordinate response efforts to ATO attacks. Collaborative initiatives can enhance the effectiveness of fraud prevention measures and strengthen the overall security ecosystem.
- Advanced identity verification and authentication technologies: Banks can explore the use of advanced identity verification and biometric authentication technologies, such as biometrics (e.g., fingerprint, facial recognition) and behavioural analytics, to enhance the security of account access and authentication processes. These technologies provide an additional layer of protection against ATO fraud by uniquely identifying customers based on their physiological or behavioral characteristics.
- Advanced fraud detection systems: Banks can leverage advanced fraud detection to develop sophisticated fraud detection systems capable of analyzing large volumes of data and detecting complex patterns indicative of fraudulent activity. These systems can help banks identify and mitigate ATO attacks more effectively, reducing the risk of financial losses and reputational damage.
By implementing these proactive measures and leveraging innovative technologies, banks can help mitigate the risk of account takeover fraud and enhance the security of their customers’ financial assets.
The importance of real-time fraud detection and prevention
Real-time fraud detection and prevention serve as critical pillars in the defense against account takeover (ATO) fraud, offering banks the ability to swiftly respond to evolving threats and protect their customers’ assets and personal information. Here’s an expansion on the importance of real-time fraud detection and prevention:
- Immediate intervention: Real-time fraud monitoring enables banks to detect suspicious activities the moment they occur, allowing for immediate intervention to halt unauthorized access attempts. This timely detection empowers banks to take proactive measures to block fraudulent transactions, reset compromised credentials, or suspend account access, minimizing the impact of ATO attacks on customers.
- Mitigation of potential losses: By identifying ATO fraud in real-time, banks can mitigate potential financial losses associated with unauthorized transactions or fraudulent activities. Rapid detection enables banks to freeze accounts, reverse unauthorized transactions, or implement additional security measures to prevent further unauthorized access, preserving the financial well-being of their customers.
- Identification of unusual patterns: Real-time monitoring enables banks to identify unusual patterns or anomalies indicative of ATO fraud, such as sudden changes in account behavior or unexpected login attempts from unfamiliar locations. By analyzing transaction data, login activity, and user behavior in real-time, banks can flag suspicious activities for further investigation, helping to identify and prevent ATO attacks before they escalate.
- Immediate alerts and investigation: Real-time fraud detection systems trigger immediate alerts in response to suspicious activities, prompting banks to initiate thorough investigations into potential ATO incidents. These alerts prompt security teams to review transaction logs, analyze user activity, and assess the risk of fraudulent behavior, enabling swift action to prevent further harm and safeguard customer accounts.
- Proactive measures and rapid response: Real-time fraud detection empowers banks to take proactive measures and implement rapid response mechanisms to counter ATO attacks effectively. Banks can deploy automated fraud prevention tools, such as rule-based systems or machine learning algorithms, to detect and block suspicious activities in real-time, bolstering their defenses against evolving fraud tactics and ensuring a timely response to emerging threats.
- Protection of financial assets and personal information: By leveraging real-time fraud detection and prevention measures, banks can protect their customers’ financial assets and personal information from unauthorized access and misuse. Rapid intervention helps to mitigate the risk of financial loss, identity theft, and fraud-related damages, preserving the trust and confidence of customers in their banking institutions.
In conclusion, real-time fraud detection and prevention are indispensable components of a robust security strategy for banks, enabling swift detection, intervention, and mitigation of ATO fraud. By investing in advanced monitoring technologies and proactive response mechanisms, banks can effectively combat ATO attacks and safeguard the financial well-being and privacy of their customers.
How Udentify – fraud.com can help
Udentify provides a complete solution to any business to prevent account takeover fraud. Udentify provides ID verification and authentication of your customer, user, business partner, patient, or student within seconds. Through liveness detection, Udentify can drastically prevent ATO fraud. Below are some of the ways in which Udentify can help you:
1. User digital onboarding
3. Passwordless authentication
4. KBA replacement
5. KYC & AML compliance
6. Strong Customer Authentication (SCA)
7. Fraud prevention