Identity is critical in our day-to-day lives. We use it to access our bank accounts, sign contracts, purchase goods and services, vote, and much more. With the growth of the Internet, we now use it to shop online, connect with friends and family, and manage our finances. Before we can carry all these activities and many more we go through a process of identity verification or identity proofing.
The importance of identity verification (IDV) has grown exponentially with this increase in online activity. Organisations of all types carry identity verification to verify the real users and stay away from the fraudsters.
Today’s fraud-riddled and compliance-based environment has made it necessary to take extra steps when conducting business. Whether you’re a merchant selling goods or services, a bank or financial institution of any size, or an individual providing professional services, you need to be sure that the person you’re dealing with is who they say they are. That’s where identity verification comes in.
Identity verification is not a new concept. We’ve been using it in some form or another since the days of the ancient Egyptians. In this article, we’ll explore how the modern world of identity verification works and the benefits it provides.
Table of Contents
ToggleWhat is Identity Verification?
Simply put, identity verification is the process of confirming that someone is who they say they are. In the physical world, this process is typically done with a government-issued ID, like a driver’s license or passport.
Various factors go into verifying someone’s identity, but it always revolves around unique identifying information. It could be something as simple as an email address (which isn’t very secure) or biometrics like a fingerprint or a face. We all have unique identifying information, and that’s what ID verification is all about: using that information to confirm someone’s identity.
At its core, we could compare it to how detectives use DNA to identify a suspect. They start with some basic information and then try to match it up with what they already know. The more they have, the easier it is to identify someone without a doubt.
What is digital Identity Verification?
In the modern world, identity verification has become much more complex. With the increase in online activity and the proliferation of personal data, there’s a greater need to confirm someone’s identity electronically. Here’s where digital identity verification slightly adapts the traditional process.
Digital identity verification is the process of confirming someone’s identity using electronic means. It slightly differs from traditional identity verification because it relies on digital data and systems instead of in-person interactions with physical documents.
However, the goal is still the same: to confirm that an individual’s perceived identity aligns with their real-world identity. Since the Internet makes it easier for people to assume false identities, digital identity verification has become an essential part of doing business online.
How is Identity Verification done, and why is it needed?
In most cases, government entities like the Social Security Administration (SSA) in the US, the Driver and Vehicle Licensing Agency (DVLA), or HM Government in the UK are responsible for issuing physical ID documents like driver’s licenses or National Passports. These organisations are recognised as official sources of truth and are therefore trusted to verify someone’s identity accurately.
Each individual in a country will be assigned a unique identifier, like a social security number in the US or a national insurance number in the UK. In the case of a driver’s license, this number will be included on the document itself.
During identity verification, users will provide their personal information, like their name, date of birth, and address. Their unique identifier can be read with cutting edge technology like optical character recognition (OCR) or Near-Field Communication (NFC). This information will then be cross-referenced with official data to confirm that the piece of ID being presented is authentic.
What is Identity Verification used for?
Identity verification is used for a variety of purposes, both personal and professional. Here are a few examples:
Required by law
In some cases, identity verification is required by law. For example, banks are required by the US Patriot Act to verify the identities of their customers before opening an account. This measure is to prevent money laundering and other illegal activities.
As we saw with the rise of cryptocurrencies, people can use anonymous digital transactions to facilitate all sorts of illicit activities. Hence, exchanges now need to keep tabs on their customers and where the funds come from.
Prevent fraud
We can also use identity verification to prevent fraud, especially identity fraud. Fraudsters are all over, and they use stolen credit card information to make fraudulent purchases. Organisation can verify the identity of their customers to ensure that the person making a purchase is actually the owner of the credit card.
Identity verification is also relevant for subscription services, like streaming platforms or online dating sites. Some of these companies must verify that each customer only has one account to prevent people from sharing passwords and circumventing the paywall.
Protect users’ data
Another important use case for identity verification is to protect users’ data. In order to comply with data privacy regulations like GDPR, businesses need to be able to verify the identity of their customers before collecting or processing their data. That ensures that only people who have given explicit consent have their data collected and stored.
Data breaches are becoming more and more common, so it’s important for businesses to take measures to protect their customers’ data.
Security purposes
Identity verification can also be used for security purposes, like when accessing a building or logging into a computer system. In these cases, the goal is to ensure that only authorised people are able to access the restricted area or system.
How does Identity Verification work?
There are a few different ways this process can be carried out, but the most common is through an identity verification service. These services are usually provided by government agencies or private companies that have been authorised to access official records. The ID verification working principle is based on the fact that each person has a unique identifier, which the government usually assigns.
They will typically have a database of all the individuals in a country, along with their associated information and unique identifiers. When a user wants to verify their identity, they will provide their personal information and ID number to the service.
The service will then confirm that the information matches what’s on file and return a result indicating whether or not the user has been successfully verified. ID verification working logic comes down to cross-referencing the data provided by the user with official records.
What are the types of Identity Verification?
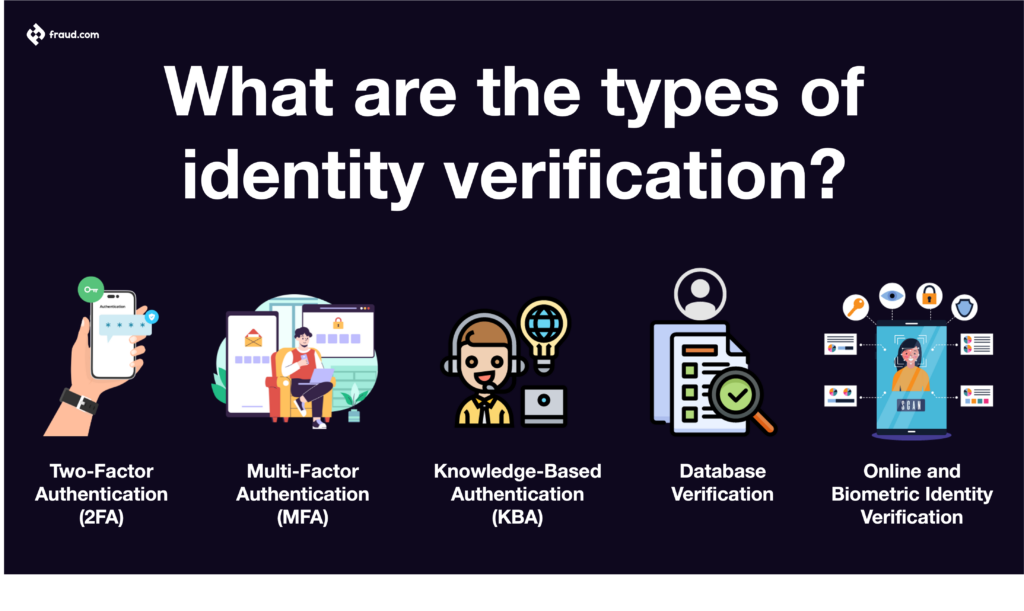
Now that we know what ID verification is and how it works, let’s take a look at the different types of identity verification and identity authentication.
Two-Factor Authentication (2FA)
2FA is often used for sensitive applications, like online banking or email. It’s also becoming more common for social media and other less sensitive applications. The goal of 2FA is to make it more difficult for someone to gain access to a user’s account, even if they have the password.
One of the most common types of ID verification is two-factor authentication or 2FA. This process requires two different pieces of information to verify the user’s identity. The first piece is something the user knows, like a password or PIN, while the second piece is something that the user has, like a smartphone or security token.
Multi-Factor Authentication (MFA)
Multi-factor authentication, or MFA, is similar to 2FA but with more than two factors. The goal of MFA is to make it even more difficult for someone to gain access to a user’s account. MFA can be used with a variety of different factors, but the most common are:
● Something the user knows: password, PIN, security question
● Something the user has: smartphone, security token
● Something the user is: fingerprint, voiceprint, iris scan, face
Knowledge-Based Authentication (KBA)
The only place safe from hackers is your own brain. By using the intimate knowledge only you should know, like the name of your first pet or your mother’s maiden name, businesses can be confident the person on the other side of the computer is who they say they are.
This type of authentication is called knowledge-based authentication, or KBA, and it’s one of the most popular methods used today.
KBA works by asking the user a series of questions that only they should be able to answer. These questions can be about their personal history, financial history, or anything else that would be difficult for someone else to guess.
Database Verification
As mentioned above, one of the most common methods for identity verification is cross-referencing the user’s information with official records. This can be done with a variety of different databases, including:
● National ID databases usually contain information like name, date of birth, and ID number.
● Electoral roll databases contain information about registered voters in a country.
● Credit bureau databases contain information about an individual’s credit history.
● Utility databases contain information about an individual’s utility bills (electricity, gas, water, etc.).
Database verification is often used in combination with other methods, like 2FA or KBA.
Online and Biometric Identity Verification
Online and biometric identity verification are two of the newest methods for identity verification. They are also two of the most effective.
Online identity verification refers to the process of verifying someone’s identity online, without the need for any in-person interaction. This is usually done through secure methods like cryptographic signatures and digital certificates.
On the other hand, biometric identity verification is the process of verifying someone’s identity using their physical characteristics, like their fingerprint, iris scan or facial biometrics. This is usually done with a biometric scanner, which is a device that can read and store biometric data.
How to verify an identity in seconds
The problem with traditional identity verification methods is that they can be slow and cumbersome. Sometimes, they even require physically mailing documents, which can take weeks. Udentify aims to change that.
Udentify is an online platform that allows you to verify someone’s identity in seconds without the need to do it physically with the organisation carrying the verification. All you need is a a mobile device with a camera to capture your ID and your face. That’s it! Using advanced AI technology, Udentify can match the ID with your face as fast as 13 seconds.
Not only is Udentify fast, but it’s also extremely accurate. In fact, it has 99.9% accuracy, which is the highest in the industry. Our proprietary technology can detect even the slightest changes in someone’s appearance, a powerful addition is having liveness detection, so no fraudster can spoof the live facial characteristics of the user.
Udentify also integrates seamlessly with your existing systems. Our SDK makes it easy to add identity verification to your website or app. And our API allows you to verify someone’s identity in real-time, without the need for any extra infrastructure. Plus, we have a Udentify app coming soon!
What are the benefits of Identity Verification?
Identity verification has many benefits, both for businesses and individuals.
For businesses, identity verification can help to reduce fraudulent activity, like chargebacks and account takeovers. It can also help to improve customer experience by making it easier for customers to sign up and log in to your website or app.
For individuals, identity verification can help to protect their online accounts from being hacked. It can also help you to avoid being scammed or phished. And it can help you save time proving your identity online, for things like opening a bank account or applying for a loan.
Overall, identity verification is a powerful tool that can help to improve security, customer experience, and compliance.
Identity verification regulations and standards
Depending on the country or industry, there are many different identity verification regulations and standards. Some of the most common regulations are KYC (Know Your Customer), AML (Anti-Money Laundering), and GDPR (General Data Protection Regulation).
● KYC is a regulation that requires businesses to verify the identity of their customers. This is usually done when a customer opens an account or starts using a service.
● AML is a regulation that requires businesses to prevent and detect money laundering. It includes things like screening customers for suspicious activity and reporting any suspicious activity to the authorities.
● GDPR is a regulation that requires businesses to protect their customers’ personal data. GDPR is known mainly for enforcing consent from customers before collecting their data and ensuring that data is stored securely.
Identity verification can help businesses to comply with all of these regulations. Failure to comply with these regulations can result in heavy fines or worse, so it’s essential to ensure that you’re using a compliant identity verification solution.
Udentify is compliant with all major identity verification regulations and standards, including KYC, AML, and GDPR. We are also ISO 30107-3 certified, which is the highest standard for information security.
How can Identity Verification impact your business?
A wide scope of industries can benefit from real-time ID verification services, including but not limited to:
Banking: From loans and credit products to fraud prevention, banks rely on customer identity verification to protect their interests.
Gaming: Online gaming companies use ID verification to prevent underage gambling and to comply with gambling regulations.
Cryptocurrency: Crypto exchanges are now required to comply with KYC/AML regulations, so they use ID verification to prevent money laundering and fraud.
Healthcare: The healthcare system is known to be overwhelmed with data breaches. To protect patients’ data, many healthcare organisations are now using ID verification.
Travel: Travel agencies can use ID verification to facilitate the booking process and to comply with travel regulations.
Insurance: Insurance companies have strict KYC requirements and use ID verification to prevent fraud and money laundering.
Dating: The rise of catfishing has made online dating riskier. Many dating sites and apps now use ID verification to protect users and enhance their trustworthiness.
E-commerce: E-commerce businesses use ID verification to protect their bottom line from fraud and chargebacks.
Government: Government agencies use ID verification for things like passport control, voting, and benefits claims.
Our Identity Verification Solution – Udentify
As you can see, identity verification can significantly impact your business, no matter what industry you’re in. If you’re not using ID verification, you could be missing out on essential compliance requirements, customer trust, and fraud protection.
Udentify offers a wide range of ID verification services that you can customise to fit your specific needs. We enable your customers to authenticate via voice, biometrics, documentation upload, live photos, and much more. Whether you need real identity verification via NFC / OCR & AI identity proofing & authentication, we have a solution for you.
Get in touch with us today to learn more about how we can help you verify your customer’s identities in real-time.